unless something really bad happens in the country, wouldnt it be impossible to put someone in prison for breaking a law that didnt exist you did the action?
yeesh, this’ll age like rotten eggs.
unless something really bad happens in the country, wouldnt it be impossible to put someone in prison for breaking a law that didnt exist you did the action?
yeesh, this’ll age like rotten eggs.
I wish you the best of luck when your health insurance rejects your life saving operation because, “you were informed of your genetic predisposition to x and did not take preventative actions for n years.”
while you’re dealing with your own mortality, you’ll also be coming to terms with your own ignorance that put you in that situation.
but don’t worry, you’re young, you’ll live forever.


I always knew he was a piece of shit because of how white he is and how much support fox gave him. – cynical man
as a full stack dev, everything you said has offended me.
port 20 is used for FTP, unless you were using FTP, then go right ahead. Guessing that since you didn’t know the protocol you were not using FTP.
port usage reservations are incredibly important to ensure that the system is running within spec and secure. imagine each interface like a party telephone line and the ports are time slots.
your neighborhood has reserved specific times (ports) for everyone to call their relatives. if you use the phone not in your slot (port) your neighbors might get pissed off enough to interrupt your slot. and then it’s just chaos from there.


I agree but until you’re in the same situation you have no idea what you’ll do.
brain chemistry is weird and makes you do the dumbest things in dangerous situations.
monkey brain goes brrrrrrr.


had to do it. it’s all I could see from the photo in the article.



let’s assume you’re correct. there’s still irrefutable evidence that she did the actions that lead to charges to be filed against her.
wouldn’t what she did be considered terrorism then? it was an act thats purpose was to inflict fear and chaos on the community and destabilize the local government.
if she was tried as a terrorist, and I believe she should have been, she would have been looking at life in prison.
so, is she a criminal or a terrorist?


it’s Ryan Hall y’all!


now you know why


this is great! now we can argue in court, “if it cannot be owned, how can it be stolen?”


“I’m rubber, you’re glue. what you do bounces off me and sticks to you.”
that’s basically what he said.
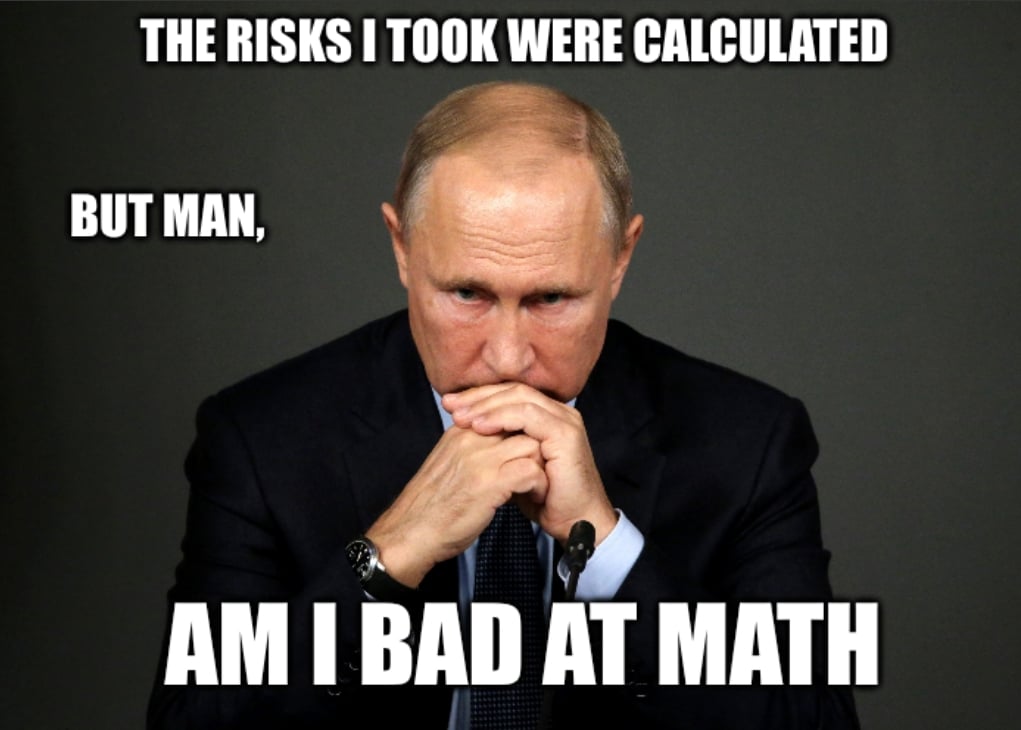
what a desperate little bitch. he can’t win against a war with a well stocked and trained army so now he has to resort to threats he can barely deliver on.
your threats are 1 out of 6 stars you basic bitch.


if it’s citrix you used to be able to modify the local connection config file to allow access to the clipboard regardless of what the server allowed.
been a few years since I needed to do it, but it was possible at one time.


that’s so easy! /s


wow that only took like 4 years to do.
it’s going to be another 10 years before they see a dime though.
oh the wheels of justice are moving. watch as they roll over the victims and blame the driver, father time.


technically any vehicle can be remotely shut down if you’re high enough on a wanted list.
just ask Ayman al-Zawahiri, wait… you can’t.


I got a Note 2 at launch and was showing it off at work to people interested in it.
someone asked about the background and where I got it. said I took it and left it at that.
took the pic of the top of my bathroom trashcan while dumping some toxic waste.
pic is the same trashcan now, like me it’s a bit dented, dirty, and doesn’t open as well as it used to. but, it still works.

“like two turds on a blanket.” – Jack Sparrow or some shit
“they didn’t come for me.”
what a damn fool.